Safeguarding your VPN
With the recent and sudden shift in global workforce culture, remote IT pros require advanced tools to sustain their oft-robust workflows.
What is a VPN?
A virtual private network (VPN) is a specialized technology for online privacy and security. It operates along an IP tunnel – a virtual point-to-point link between a pair of nodes separated by an arbitrary number of networks. It is particularly beneficial to public WiFi, which is often not password protected.
A VPN can be likened to a “bulletproof vest” for internet connectivity – it encrypts exchangeable internet data, and enables and safeguards private or anonymous browsing. VPN protection renders instant messages, login information, social media, and other forms of data unintelligible, which severely handicaps cybercriminals.
VPNs are most effective when paired with antivirus software. Antiviruses keep your devices free from infection by combating malware and other forms of cyberattack. VPNs, on the other hand, cloak your data by encrypting it during its journey between your device and network. Simply put, an antivirus operates at the device level; while a VPN operates at the network level (e.g., against packet sniffers, compromised routers, ISP snooping).
VPN Security
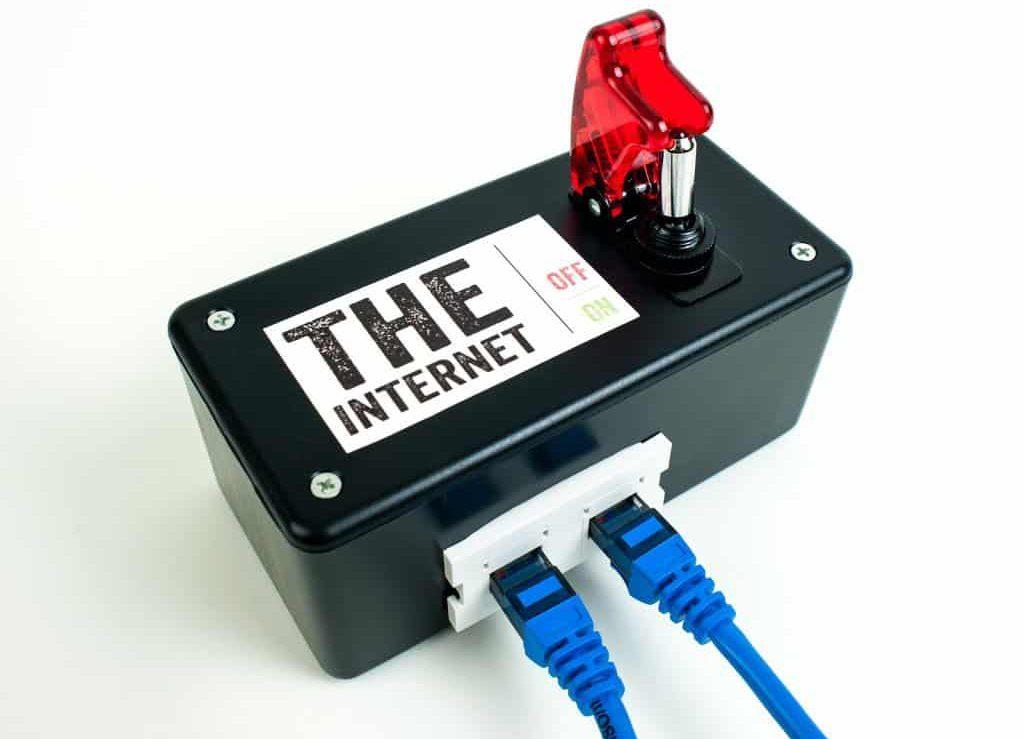
If your VPN server has disconnected or gone down without warning, your data safety can be sustained with a “kill switch”. The VPN kill switch adds an extra layer of protection that blocks data transmission until the VPN connection is re-established. By shutting down your internet connection, it prevents the exposure of your unencrypted data; and ultimately serves as an “alert” for you, and your team, to reconnect the VPN.
VPN protection can be further reinforced with a firewall. Successful VPN and firewall integration is contingent upon the arrangement of the VPN location, firewall, remote network, and Internet connection. The most common and effective arrangements are as follows:
- Individual Computer to Remote Network via VPN through Firewall to Internet
- Individual Computer to Remote Network via Firewall to VPN to Internet
- Individual Computer to Remote Network via Firewall and VPN Combination in One Device to Internet
NOTE: A firewall behind the VPN will ensure that any threats to the VPN box will be circumvented, thus ensuring a clean connection for the end user. For more information on VPNs, and to debunk any myths, visit extrascrew.com.

Trusted Tech Team is an accredited Microsoft CSP Direct Bill Partner, carrying multiple Solutions Partner designations and the now-legacy Microsoft Gold Partner competency. Based in Irvine, California, we report trends affecting IT pros everywhere.
If your organization uses Microsoft 365 or Azure, you may be eligible to receive a complimentary savings report from a Trusted Tech Team Licensing Engineer. Click here to schedule a consultation with our team now to learn how much you can save today.
Subscribe to the Trusted Tech Team Blog
Get the latest posts delivered right to your inbox

