Defending Your Business Against the Rising Threat of Business Email Compromise
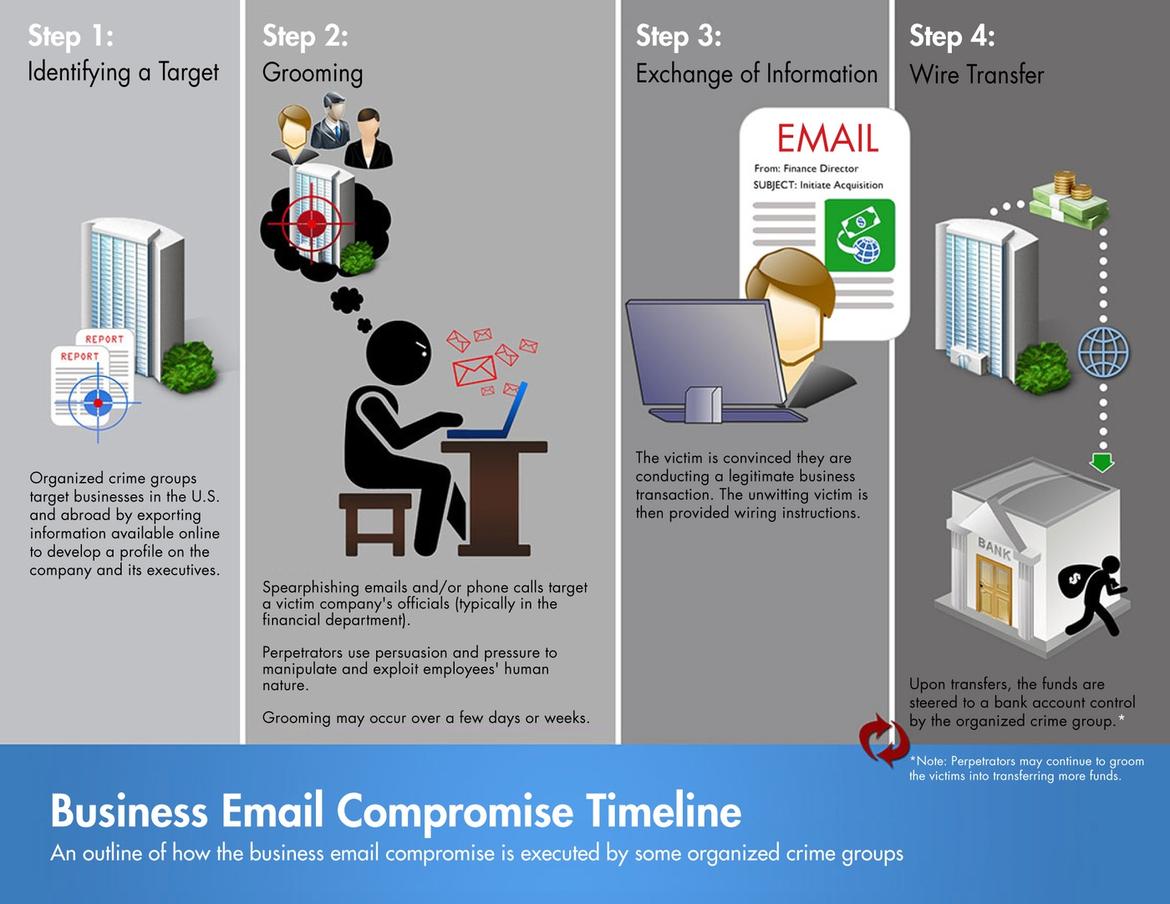
Cybersecurity is locked in a continuous race with the rising tide of online threats. Among these, Business Email Compromise (BEC) attacks stand out for their sophistication. They zero in on businesses, especially those engaging regularly with suppliers or conducting frequent wire transfer payments.
Microsoft just revealed that BEC attacks, where cybercriminals impersonate high-ranking officials to trick employees into transferring funds, have spiked by a concerning 38% compared to 2019. Not only is this an alarming trend in and of itself, but threat actors behind these attacks are also upping their game by leveraging cybercrime-as-a-service (CaaS) platforms, making their attacks even trickier to disrupt.
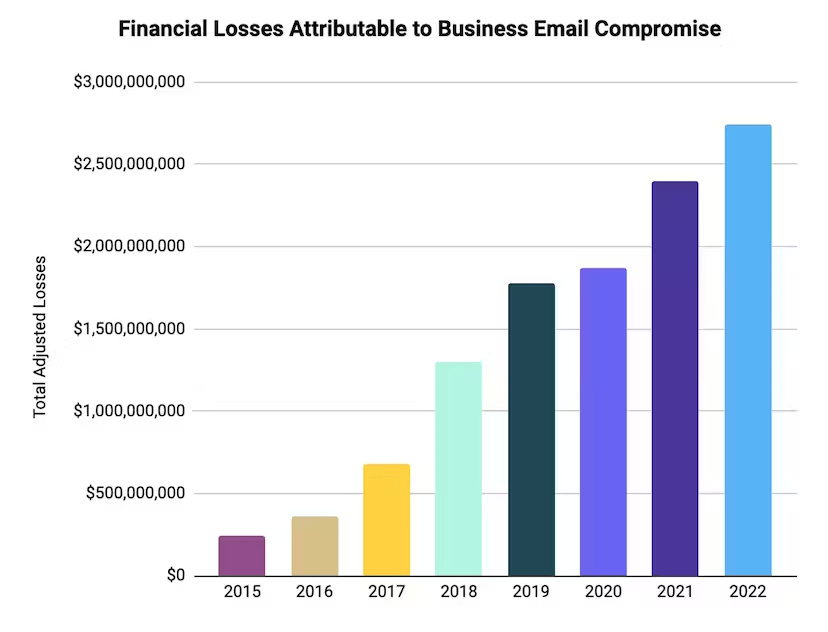
Picture this: An unsuspecting employee receives an email from their manager requesting an urgent funds transfer. The email appears legitimate - with the manager’s correct email signature and company logo. It’s a scenario that, unfortunately, played out too often in 2022, culminating in businesses suffering a staggering $2.7 billion in losses, a whopping 14.5% increase since 2020.
Source: Abnormalsecurity.com
And it doesn’t stop at financial losses. Companies hit by BEC attacks are often left grappling with reputational damage, customer distrust, and the fallout from legal repercussions. The damage is multi-faceted, far-reaching, and, at times, irreparable.
Fortifying Your Defense
So, in the face of this rising threat, how can you equip your business with a digital suit of armor? Microsoft recommends adopting a multi-faceted approach.
This begins with implementing secure email solutions and adopting principles like Zero Trust and automated identity governance to reinforce your digital identities. Also, ensure the use of secure payment platforms that offer an additional layer of protection for your transactions. Complement these measures by implementing two-factor authentication and scrutinizing email addresses and URLs for any hint of discrepancy. These checks can be critical in detecting fraudulent communication before it wreaks havoc.
The Human Firewall: Why Training Matters
Your technology can only be as smart as the people using it, which is why training is everything. Ensuring your team can recognize red flags, like unexpected requests, emails sent at an odd hour, or even a slightly altered email address, can make all the difference.
Remember, scammers often exploit the high volume of email traffic within businesses. All it takes is one distracted moment, one overlooked detail, and the scammer’s mission is accomplished.
Source: FBI.gov
Hit By a BEC Attack? Here’s What You Do
If you find yourself a victim of a BEC scam, swift action is the order of the day. Report the crime to your financial institution immediately. Contact your local FBI field office and file a complaint with the FBI’s Internet Crime Complaint Center (IC3). Every moment counts.
Stay Vigilant, Stay Secure
The surge in BEC attacks is a grim reminder of the evolving cybercrime landscape, marked by increasing sophistication and persistent threats. But remember, while the scams continue to morph, so can your defense strategy.
In the face of these threats, awareness, preparedness, and a robust cybersecurity strategy are your best allies. Consider regular cybersecurity audits. Foster a culture of continuous learning and awareness about the latest threats in your organization. Above all, remember that in cybersecurity, as in life, forewarned is forearmed.
Trusted Tech Team is an accredited Microsoft CSP Direct Bill Partner, carrying multiple Solutions Partner designations and the now-legacy Microsoft Gold Partner competency. Based in Irvine, California, we report trends affecting IT pros everywhere.
If your organization uses Microsoft 365 or Azure, you may be eligible to receive a complimentary savings report from a Trusted Tech Team Licensing Engineer. Click here to schedule a consultation with our team now to learn how much you can save today.
Subscribe to the Trusted Tech Team Blog
Get the latest posts delivered right to your inbox