Microsoft Graph API v1: A Game-Changer for Attack Simulation Training
Imagine being able to anticipate and counter cyberattacks before they happen. The Microsoft Graph API v1 works to accomplish exactly that. Now Generally available, it offers a realistic and efficient way to test and strengthen an organization’s defenses by simulating a range of cyber threats, helping organizations identify vulnerabilities, train staff, and refine their defense strategies. It’s like having a crystal ball that actually works, minus the mystical fog and cryptic predictions.
Who Stands to Benefit?
The Microsoft Graph API v1 is a boon for IT professionals, cybersecurity teams, and anyone responsible for an organization’s digital health. Whether you’re a tech giant, a budding start-up, or a non-profit, if you’re operating in the digital realm (which, let’s face it, is pretty much everyone these days), this is relevant to you.
The Nitty-Gritty: Creating and Managing Simulations
Ready to get your hands dirty? Using the Graph API v1, you can concoct a variety of attack simulations. Think of it as being the director of your own cyber-thriller. You can script different attack scenarios – from phishing to password attacks – and see how your team responds in real time.
Here’s a simplified breakdown:
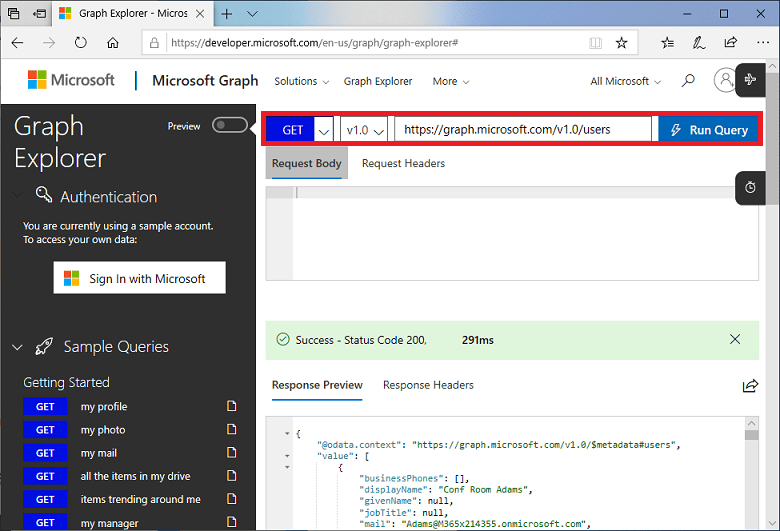
- Access the API: First, gain access to the Graph API through Microsoft’s platform.
- Craft Your Scenario: Choose the type of attack you want to simulate. Phishing email on a Monday morning, anyone?
- Target Audience: Decide who in your organization will be part of this simulation. No, you can’t choose your boss every time.
- Launch and Observe: Initiate the simulation and watch how your team reacts. Do they spot the threat, or do they take the bait?
- Analyze and Educate: Post-simulation, it’s time to analyze the results and provide feedback. Turn those oops moments into teachable ones.
Hypothetical Scenarios: The Graph API v1 in Action
- The Classic Phishing Test: You send out a simulated phishing email to see if employees can spot it. Those who click on the dubious link are redirected to a training module.
- The Password Heist: Simulate a brute force attack on user passwords. Discover who’s using ‘password123’ and kindly suggest they up their game.
- Insider Threat Simulation: Mimic the actions of a disgruntled employee trying to access sensitive data.
- Ransomware Drill: Simulate a ransomware attack to test your organization’s response time and recovery procedures.
- Cross-Departmental Crisis: Run a cross-departmental simulation involving multiple teams.
Cyber threats are now as common as coffee spills, which is why tools like Microsoft’s Graph API v1 for attack simulation training aren’t just fancy add-ons; they’re necessities. It’s about being proactive rather than reactive. Stay safe out there!
To stay informed on Microsoft’s latest updates and announcements, subscribe to the TTT newsletter and get all things Microsoft delivered straight to your inbox. If you’re concerned about your product lifecycles affecting your additional custom line-of-business software, contact Trusted Tech Team, and we’ll gladly help you.
Trusted Tech Team is an accredited Microsoft CSP Direct Bill Partner, carrying multiple Solutions Partner designations and the now-legacy Microsoft Gold Partner competency. Based in Irvine, California, we report trends affecting IT pros everywhere.
If your organization uses Microsoft 365 or Azure, you may be eligible to receive a complimentary savings report from a Trusted Tech Team Licensing Engineer. Click here to schedule a consultation with our team now to learn how much you can save today.
Subscribe to the Trusted Tech Team Blog
Get the latest posts delivered right to your inbox

