How to Protect your Business Against Cybercrime During the Holiday Season
’Tis the season of joy and cheer – but while we raise our cups with holiday glee, let us not forget that businesses are at an Enhanced Risk from cyberattacks this time of year. Working from home, decreasing in-office tech staff, and leaving servers unmonitored: these realities make it even more imperative to protect your company against digital hazards as 2022 rounds out for good. Join us in celebrating a safe and secure 2023 by taking some steps to stay safeguarded during the holidays.
To tackle the holiday season’s cyber vulnerabilities, first, understand why they occur in the first place. Businesses often experience cybersecurity fatigue during the holidays, which is understandable since everyone is expected to stay on high alert throughout the year. Trying to remember password security protocols and keep up with all the security awareness training courses can be exhausting. Unfortunately, relaxing cybersecurity posture and increasing holiday spending create the perfect conditions for threat actors to strike. Therefore, it’s vital to remind yourself that the fatigue you’ll experience when a security crisis hits you outweighs any fatigue you’re undergoing by adhering to your organization’s security measures.
Here are five simple security measures you can take immediately to shore up your defenses.
Halt Significant Changes in Your Security Stack
Making significant changes to your security stack during the holiday season can be risky since it opens up your system to potential new vulnerabilities that cyber criminals could exploit. If any issues arise due to these changes, they may go unnoticed due to reduced staffing or oversight. Moreover, suppose you don’t have enough personnel to thoroughly test any new changes before they are implemented. In that case, you could unwittingly create further problems compromising your system’s security in the long run.
Monitor all Traffic in the Security Operations Center (SOC)
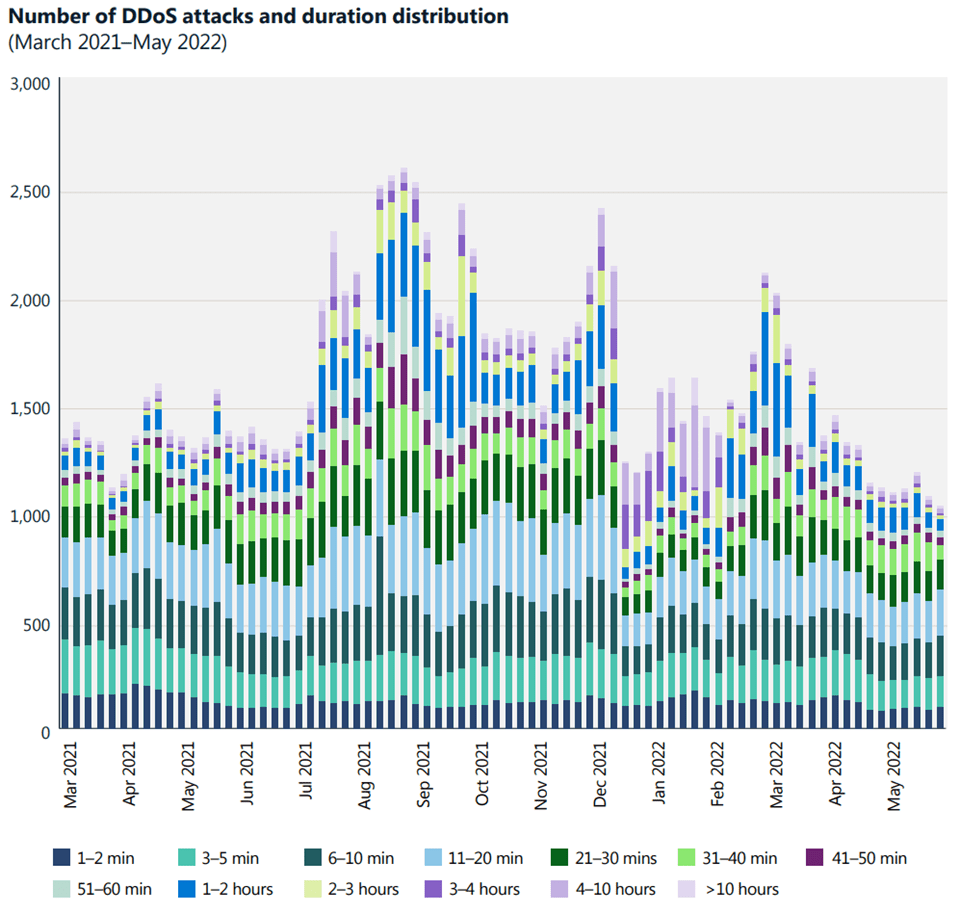
Identifying which applications within your organization are connected to the internet will help you evaluate potential risks and vulnerabilities. That includes understanding normal behavior so that you can identify issues more efficiently. Use Azure’s monitoring services and best practices for guidance. Azure DDoS Protection provides always-on traffic monitoring, automatic mitigation when attacks are detected, adaptive real-time tuning, and complete visibility on DDoS attacks. Enable protection for virtual networks with applications exposed to the internet (e.g., Application Gateway, Load Balancer, Virtual Machines) and resources that require protection against DDoS attacks (e.g., Firewall).
Create a DDoS Response Strategy
Since Distributed Denial of Service (DDoS) is one of the most widespread threats during the holiday season, it’s crucial to have a solid DDoS response strategy. Create and assign clear roles to an experienced team that can quickly identify, mitigate, and monitor attacks. Test your plan regularly to plug any holes in the defenses before trouble arises.
Run Attack Simulations Regularly
DDoS simulations are a great way to gain insight into the strength of your DDoS defenses. They can help you understand what you may need to upgrade security-wise and how well-equipped your capabilities truly are. Furthermore, they can help you identify and address any potential loopholes in risk mitigation processes so that you can rest assured knowing they won’t be exploited during attacks. Various services can help you simulate a DDoS attack on your Azure environment. Consult your team on which service meets your organization’s needs.
Establish Internet of Things Best Practices for Employees at Home
Devices with internet connectivity have been rising in popularity as gift items. But although they make for thoughtful gifts, they present security risks - especially when paired with remote workplace devices. Communicating with your employees on how to safely handle such devices can help protect your network from potential breaches.
In addition to the above steps, it’s important to remember the basics:
-
Update Software & Operating Systems Regularly
Keeping your software and operating systems up-to-date is the surest way to protect your business from cyber threats. Regular updates often include patches to known vulnerabilities, protecting you from most cyber threats.
-
Educate your Employees
Train your employees on security best practices such as avoiding suspicious emails or downloads, not sharing confidential information online, and identifying advanced social engineering tactics. Encourage them to report anything suspicious they may encounter while working remotely, and reward them when they address legitimate threats.
-
Utilize Strong Authentication
Implement multi-factor authentication (MFA) for all accounts where possible. That means that users will have to enter additional information beyond their username and password to log into their accounts (such as a prompt sent to an authentication app on their phone). MFA provides an extra layer of security that makes it difficult for attackers to access accounts even if they have obtained login credentials through other means.
Lastly, remind your employees and colleagues to be careful with what they share on social media: never post information that may assist others in accessing your accounts (location, phone number, birth date, etc.)
It’s more crucial than ever for businesses to be aware of potential cybersecurity threats and take steps to protect themselves against them. By following these tips, you can easily elevate the security of your business and ensure it is well-prepared for whatever challenges may arise. Happy Holidays!
Trusted Tech Team is an accredited Microsoft CSP Direct Bill Partner, carrying multiple Solutions Partner designations and the now-legacy Microsoft Gold Partner competency. Based in Irvine, California, we report trends affecting IT pros everywhere.
If your organization uses Microsoft 365 or Azure, you may be eligible to receive a complimentary savings report from a Trusted Tech Team Licensing Engineer. Click here to schedule a consultation with our team now to learn how much you can save today.
Subscribe to the Trusted Tech Team Blog
Get the latest posts delivered right to your inbox

